Category: privacy
RT.com interview on ‘secure’ smartphone apps
On Friday October 17th I was interviewed by Russia Today on the security of ‘secure’ smartphone apps that turn out to not be so secure. After 18 months of Snowden revelations that should be not news but for the Guardian newspaper it is.
The other IT from another Europe
Also on Consortium News and Huffington Post
 Over the last 10-15 years public IT in Europe has not developed in line with public interests, nor does it guarantee the fundamental rights of citizens such as privacy and freedom of expression. Tremendous opportunities in the field of economic development and employment have also been missed. Europe effectively outsources much of its information processing (software & services) to foreign parties at the direct cost of hundreds of billions of Euros (typically around 1% of GNP). The opportunity-cost to local economic growth and employment opportunities are much greater than that. Even more costly than either of these is the de-facto handing over of control of data of governments, businesses and individual citizens to foreign spies who use it for political manipulation, repression of citizens’ freedoms and industrial espionage. Although the warnings about the negative consequences of current policies date back at least 15 years, these aspects have been documented in irrefutable detail over the last year by the revelations of Edward Snowden. 12 months later there has not even been the beginning of a policy response.
Over the last 10-15 years public IT in Europe has not developed in line with public interests, nor does it guarantee the fundamental rights of citizens such as privacy and freedom of expression. Tremendous opportunities in the field of economic development and employment have also been missed. Europe effectively outsources much of its information processing (software & services) to foreign parties at the direct cost of hundreds of billions of Euros (typically around 1% of GNP). The opportunity-cost to local economic growth and employment opportunities are much greater than that. Even more costly than either of these is the de-facto handing over of control of data of governments, businesses and individual citizens to foreign spies who use it for political manipulation, repression of citizens’ freedoms and industrial espionage. Although the warnings about the negative consequences of current policies date back at least 15 years, these aspects have been documented in irrefutable detail over the last year by the revelations of Edward Snowden. 12 months later there has not even been the beginning of a policy response.
 It could all have been so different …
It could all have been so different …
In the first 21 months of the 21st century, the dot-com bubble burst and then three skyscrapers in New York collapsed. Between these two events a largely forgotten report to the European Parliament appeared in the summer of 2001. This report described the scale and impact of electronic espionage in Europe by the U.S. and its ‘Echelon’ partners (Canada, UK, Australia and New Zealand). Besides a detailed problem analysis, the report also gave concrete examples of IT policies that governments could take to significantly limit foreign intelligence spying on Europe.
In the same period was U.S. government won one of the largest anti-trust cases its history, against Microsoft, and the EU followed this victory by launching a similar case that would also be won leading to the highest fine to a company for economic crimes in the history of the EU.
It was against this background that thinking about strategic versus operational aspects of IT in the public sector changed. The report on Echelon made it clear that reducing IT into a merely operational exercise had disastrous consequences on the sovereignty of European states with respect to, in particular, the United States (and perhaps in the near future, China, other technically capable countries or non-state organizations). The economic consequences of industrial espionage against many high-tech and R&D-intensive companies became a major concern for the government.
The IT policy of governments would from 2002 onwards be based first on the political principles of a democratic and sovereign state. This not only meant a very different policy in the field of technology selection and procurement, but also the balance between outsourcing versus in-house expertise and required an extreme degree of transparency from all suppliers. Open data standards for public information were required, and non-compliance resulted in severe penalties (although public ridicule from 2009 onward was generally the most effective). These new frameworks for public IT created a new market for service providers who based solutions on so-called ‘Free Software’ (previously better known as ‘opensource’). The high degree of transparency both in project implementation as the technology itself made for a well functioning market and made recycling of (parts-of) systems the norm. Spending on software fell sharply and the freed up budget was used for the recruitment of highly qualified IT workers under conditions that could compete with the offerings of market.
The full transparency with respect to both the IT projects and the tech itself, combined with a depth of expertise within the government, changed the market for public software and IT services. Quality rose steadily while prices remained permanently under pressure. Since all service providers had full access to all software used in government (with only a few exceptions in defense, justice and home affairs), there was a very open playing field where all providers were expendable (and those who performed below par were replaced regularly).
In addition, computer and IT education from kindergarten to university studies was fundamentally revised. Basic understanding of the operation of computers and information networks became as normal as reading and writing. From 2006 every 14 year-old was taught in school how to encrypt email and what the disadvantages were of using software whose source codes are not published. Through this awareness among young people in Europe the adoption of social media occurred very differently than in the U.S.. Young people not only had end-user skills but real understanding about what was happening to their information when sending a message or upload a photo to websites. Being careful with your private information was considered cool. The social media landscape was not dominated by a handful of U.S. companies, instead there was a landscape of federated services such as Diaspora who competed among themselves but were compatible in the same way as is the case with email. These services were sometimes somewhat centralized but, just as often, completely decentralized and run on micro-servers in many people’s homes (such as the UK-invented 35 Euro RaspberryPi).
Due to the high privacy and safety awareness online crime did not have much grip on most European countries. Hardly anyone was naive enough to log on to strange domains or websites in response to a fake email that appears to come from their bank. And the use of customized secure USB drives created by various banks was accepted as obvious for any major online financial transactions. At the level of organisations high levels of expertise and a high degree of diversity in technology implementations made for robust security that was only seldom breached. The large demand for experts in well-paid jobs also kept many would-be criminals from selling their skills for more destructive applications.
This is the IT that Europe could have had if other choices were made over the last 12 years. All the knowledge and technology for these choices were available in the first months of this century. Because these choices were not made Europe has spent hundreds of billions on software licenses and services from American companies, while there were cheaper (often free), more flexible and safer alternatives available that would not operate as a foreign espionage platform. All these hundreds of billions were not not invested in European service, training, education and R&D. The economic impact may be a multiple of the roughly $1 trillion in foreign software licenses spent by Europe this century, while the social cost resulting from manipulated politicians during transatlantic negotiations on trade or environmental matters will probably never be known.
Europe still has everything it needs to develop and implement such policies. It is not too late to turn, no matter how regrettable the policy failures of the last decade and no matter how many wasted billions. Today could be the first day of such a new course. Concrete examples in the Netherlands, Germany, France, Spain the UK and many other places show that this is not only possible, but almost immediately leads to huge savings, improved safety and independence from foreign parties in future IT choices.
It’s not often that regaining national sovereignty and the restoration of civil rights can spur national innovation and employment programs simultaneously. The only thing missing is the political will to stop rewarding businesses and governments that use their technological dominance to spy on the entire world. We have nothing to lose but our chains to the NSA.
Kerckhoffs lecture: what Europe needs to do after Snowden
 At 12:30 on Friday 13th of June 2014 I will give the Kerckhoff Lecture at the Radboud Universities Kerckhoffs Institute for information security in Nijmegen in room HG00.068. For an audience of students and faculty who probably know more about the maths of cryptography than myself I will talk about the tech-policy implications of the Snowden revelations and why Europe has been doing so very, very little.
At 12:30 on Friday 13th of June 2014 I will give the Kerckhoff Lecture at the Radboud Universities Kerckhoffs Institute for information security in Nijmegen in room HG00.068. For an audience of students and faculty who probably know more about the maths of cryptography than myself I will talk about the tech-policy implications of the Snowden revelations and why Europe has been doing so very, very little.
Imagine a whistleblower releasing detailed documentary proof of a group of organisations that dump large volumes of toxic mixed chemical waste in European rivers and lakes. The documents describe in detail how often (daily) and how toxic (very). Now imagine journalists, civic organisations and elected representatives all starting furious discussions about how bad this is and what the possible horrible consequences theoretically could be for european citizens.
Now imagine that this debate goes on and on for months as slowly more documentation is published showing ever more detailed descriptions of the various compounds in the toxic chemicals and what rivers and lakes precisely they are being dumped into.
 Now imagine that no journalist, civic organisation or elected representative comes up with a single concrete and actionable proposal to stop the actual and ongoing toxic dumping or to prevent future organisations getting into the habit of illegal dumping.
Now imagine that no journalist, civic organisation or elected representative comes up with a single concrete and actionable proposal to stop the actual and ongoing toxic dumping or to prevent future organisations getting into the habit of illegal dumping.
Imagine also that both governments and public-sector organisations, including the ones responsable for health- and environmental matters continue not only to procure products and services from above organisations but also continue to give them the licences they need to operate.
Imagine that this goes on for month after month after month for a full year.
Now Imagine it turns out that the Government not only already knew about this 13 years before but also had a detailed report on practical solutions to clean up the mess and prevent future poisoning.
Imagine that.
Sounds incredible does it not?
Except this is precisely how Europe has been not-dealing with the revelations by Edward Snowden on industrialised mass-surveillance of our government & civic institutions, companies and citizens.
The EU has spent most of a year holding meetings and hearings to ‘understand’ the problem but has not produced a single word on what concrete actions could regain the right to privacy for its citizens now. This while a July 2001 report on Echelon, the NSA/GCHQ precursor program to the current alphabet soup, explained the scope of the problem of electronic dragnet surveillance and made practical and detailed recomendations that would have protected Europeans and their institutions had they been implemented. Currently only Germany has seen the beginnings of policies that will offer some protection for its citizens.
On Friday the 13th of June I will discuss the full scope of the NSA surveillance problem, the available technological and policy solutions and some suggestions about why they have not and are not being implemented (or even discussed).
Slides from lecture are here in ODF and PDF
Letter to Parliamentary Committee on Gov. IT projects
 Letter below has been submitted to the Temporary Committee on Government IT. This document is a translation from the Dutch original.
Letter below has been submitted to the Temporary Committee on Government IT. This document is a translation from the Dutch original.
Dear Members of the Committee on ICT ,
On June 1st, 2012 I was invited by your predecessors to contribute to the expert meeting of the Parliamentary Working Group on ICT projects in government. The written submission that I made at that time is here, including a video of those hearings (in Dutch).
As an IT architect but also as a concerned citizen, I have been actively involved with the IT policy of the government since 2002, focusing on the areas of electronic health records, security and open standards / open source software. On the latter issue I was the initiator of the 2002 Parliamentary ‘Motion Vendrik’ that advocated greater independence from dominant software suppliers. Last year I also served as a technical expert on the Committee of Minister Plasterk who advised on the (im)possibilities of electronic support for the electoral process.
Although this motion Vendrik from 2002 was translated into the Heemskerk Action Plan in 2007, this policy was quietly killed in 2010/11 by the lobbying power of large software vendors and the U.S. government. Even the Court-of-Audit was pressured to *not* ask certain questions in its 2011 report on the policy. Since 2002, the Netherlands has spent about 60-90 billion on foreign software, for which in many cases free, equally good or better alternatives are available. Their use is, however, actively hindered by both the Ministries of Education and Interior, as well as the VNG supported by the lobbying apparatus of major suppliers and the U.S. government.
This despite Justice Minister Donner’s 2004 letter to Parliament in response to the Motion Vendrik where he admitted that:
- the government’s dependence on Microsoft was very great;
- that this was a problem ;
- and that by introducing open standards and the use of open source that could be solved.
This dependence has since become much greater and more than one billion Euro was spent on Microsoft licenses over the last decade. That money would have paid for 10,000 man-years of expertise to migrate away from Microsoft products. A large part of the money spent would have remained in the Dutch economy and returned to the state through tax and VAT. Not that 10,000 man-years would have been needed. The Municipality of Ede did it against the odds for a fraction of the cost and now saves 92 % on software expenses (and 25% on overall budget). The rest of the government has yet to take steps. Why is an important question.
In addition to the huge amounts of money involved (the VAT ends up mostly in the Irish exchequer due to inter-EU trade to Irish headquarters of IT companies), it has also become clear in recent months thanks to Edward Snowden in particular that U.S. software is deployed as espionage infrastructure . This has practical implications. For example, the current semi-privatised infrastructure of the national Electronic Health Records system has been put under technical management of an American company and therefore falls under the Patriot Act. But the Windows PCs ( which are de facto mandatory in secondary schools) and Gmail accounts (which are necessary to follow a University course) are part of the global spy network. Similarly with the iPhones that some of you might use, about which NSA internal documents boast of the 100% success rate in automated monitoring at zero dollars cost per device.
All this means that even if IT projects according to any definition ‘succeed operationally’ these often still violate the basic rights of millions of Dutch citizens (article 12 NL – Constitution, Art 8 ECHR , Art 12 UNDHR). Examples include electronic heatth records, transportation smart cards and many information processing systems of governments that have been outsourced on foreign soil and/or to foreign companies (such as the database of fingerprints that for many years has been linked to the issue of passports).
Both the EU and the Dutch government have been aware of this problem since the summer of 2001, yet nothing has since been done in the Netherlands to ensure the privacy of citizens or the data security of Dutch public and private institutions. Indeed, much has been done by the government which has greatly exacerbated this problem.
The above points, in my view, mean that a purely ‘operational ‘ approach to project success simply does not cover all the obligations of a democratic government in its role as guardian of the rights of its citizens.
This past weekend, I have viewed the first five videos of hearings and was most impressed by the contribution of Mr. Swier Jan Miedema. He seemed to be the only person genuinely committed to getting to the heart of the problems and saying out loud what he thought (although Prof . Verhoef also make quite a few wise points). The most compelling aspect of his testimony was the obvious fear of specifically naming a commercial party. This seems to confirm what many in the Dutch IT world know: companies like Centric abuse their dominant position in local government for short-term gain including the exclusion of anyone who is a threat to those gains (here another example).
That an IT professional of such seniority has to beat around the bush with a trembling voice is typical of the situation in the ‘market’ for public ICT. Institutionalized corruption and abuse of power is more associated with a developing country than a democracy.
In the conversations with both Mr. Miedema and other experts several members of the committee asked several times if these people could not suggest what would ‘solve’ all this. As if the problem was something that could be fixed with some trick. It is worryingly obvious that (two years and 8-12 billion after the start of the Commission) there is still the idea these problems can be solved by changing project-management methodology. Based on my experience, I believe that the problem is much more fundamental. I strongly urge you to look much more widely and more deeply at the problem and to not exclude your own role as parliamentarians in this. No questions or solutions should be taboo. Even if thereby the significant economic interests of above mentioned suppliers or the job security of groups of officials/civil servants must be called into question.
Both Mr. Miedema and Prof. Verhoef expressed the view that everything that happens can be broadly explained by the incompetence that exists in both the government and its suppliers. There are however, limits to the incompetence theory. Somewhere in the process the prolonged and appalling scale of wasting money, endangering the cyber security of the Netherlands and violating the privacy of millions of Dutch citizens has been allowed (or at least not considered an important subject). The fact that the Commission itself over the last 2 + years can spend a couple of hours a week on a problem that costs hundreds of millions of Euros monthly might also be an indication of some inexplicable non-priority. There are many officials, businesses, cybercriminals and intelligence services abroad that greatly benefit from the status quo. Look especially at those who do not come to your hearings.
In the 21st century laws are made reality by software. So it no longer befits a democracy to hand over control of that software to (often foreign) commercial parties. Executive parts of government must be accountable to you ultimately and without control over the technology that underpins their work this accountability is simply not possible.
Obviously I am willing to explain myself further as to above matters.
With kind Regards,
Arjen Kamphuis
June 9th 2014: In The other IT of another Europe I commemorate one year of the Snowden/NSA scandal by describing a scenario in wich other choices were made, choices that are still open to us today…
11-02-2014, the day we fight back
Today is the 11th of Februrari 2014,“The Day We Fight Back”. We fight against out-of-control spying on our privacy as free citizens. We fight against Orwellian espionage because we know where it leads to in the end.
The text below is inspired by the speeches of Winston Churchill in during may and june 1940. While the nature of the opponents of democracy and freedom is different today the consequences of losing the fight are just as dire. Our society and the planetary eco-system is a great trouble. We need our democracies to function and our internet to be free so we can adress the great challenges of out time.
“What Cory Doctorow and Aaron Schwartz called the fight against SOPA & ACTA is over. The battle against TTP and global surveillance continues to rage on. Upon this battle depends the survival of the internet and our democracies. Upon it depends our own way of life and the long continuity of our institutions and our culture. Once again the whole fury and might of the enemies of freedom will very soon be turned on us now.
Those working towards a police state know that they will have to break us or lose this conflict. If we can stand up to them, all of the Internet may be free and the life of the world may move forward into broad, sunlit uplands. But if we fail, then the whole world, including the United States and Europe, including all that we have known and cared for, will sink into the abyss of a new corporatist Dark Age, made more sinister, and perhaps more protracted, by the lights of perverted technologies.
You ask, what is our policy? We can say: It is to hack, by server, laptop and phone, with all our might and with all the strength that Turing can give us; to wage lulz against a monstrous tyranny, rarely surpassed in the dark, lamentable catalogue of human crime. That is our policy. You ask, what is our aim? I can answer in one word: victory, victory at all cost, victory in spite of all the terror, corruption and lies.
I have, myself, full confidence that if all do their duty, if nothing is neglected, and if the best arrangements are made, as they are being made, we shall prove ourselves once more able to defend our networked homes. To ride out the storm of surveilance, and to outlive the menace of tyranny, if necessary for years, if necessary alone. At any rate, that is what we are going to try to do. That is the resolve of the hacktivists – every one of them. That is the will of free citizens, the technologists and the creatives, linked together in their cause and in their need, will defend their native internet, aiding each other like good comrades to the utmost of their strength. Victory, however long and hard the road may be; for without victory, there will be no free culture and no culture of freedom.
Therefore we shall go on to the end:
we shall fight in Europe,
we shall fight on our browsers and our operating systems,
we shall fight with stronger encryption, and secure hardware,
we shall fight with growing confidence and growing strength
we shall defend our networks, whatever the cost may be,
We shall never surrender.
Let us therefore brace ourselves to our duties, and so bear ourselves that, if the Internet and its hacker community last for a thousand years, they will still say, “This was their finest hour”.”
No go participate or organise a cryptoparty, support people developing better tools (mail, web, secure systems and all this Free-as-in-freedom Software) or ask other people if they value being able to read without being read at the same time. Privacy is a human right according to the UN Declaration of human rights and yes, you to have something to hide as well.
First they came for the trade-unionists
Originally for Consortium News – Warning! this article violates ‘Godwin’s Law ‘ in almost every paragraph. Regrettably all these violations are all based on historic facts and documented current events.
From Rick Falkvinge’s blog post:
When the famous skyline landmark building in the world’s economic center was attacked in fire and flames on that fateful, horrible day, and our elected leaders decided to go to war against terrorism under the banner of “you’re with us or against us”.
When the blame for all evil was unanimously put on people from the Middle East with their foreign religion, and all of those were made suspicious.
When patriotic new laws were passed almost immediately in the emotions from the attack, and those laws suspended most civil rights. When the word “Homeland” suddenly started being used again, after having been practically extinct.
When the country went to war, one after another, in the wake of that attack. When internment and torture camps for those middle-easterners and other unwanteds were created – outside the country borders, in order to hide what was going on from the public.
Indeed, the 1930s were a very dark time in Germany, and the Reichstag fire in Berlin set off a chain of events that might – theoretically – repeat itself.
After more than six months of revelations about the global surveillance infrastructure built by the U.S. government and its “allies” (i.e. smaller countries that believe smiling-at-the-crocodile-in-the-hope-he-eats-you-last is a good long-term strategy), many people and politicians still tout the “I have nothing to hide” attitude toward the most over-armed, hyper-intrusive super-power in human history.
In a recent New Yorker article, U.S. Sen. Dianne Feinstein, D-California, chair of the Senate Intelligence Committee, was quoted as saying: “My phone numbers, I assume, are collected like everybody else’s, but so what? It does not bother me. By the Supreme Court decision in 1979, the data is not personal data. There’s a Google Map that allows somebody to burgle my house, it’s so clear and defined, and I can’t do anything about it.”
For an elected U.S. senator to state the above is quite astonishing. Apparently a 35-year-old court decision, Smith v. Maryland, from a technologically different era is considered unalterable scripture (by a lawmaker!) and the power of the Google Corporation is simply accepted as a law of nature. Like the speed of light or the boiling point of water. What did that influential Italian political thinker from the 1920s say about the merger of state and corporate power? Wasn’t that the (political) F-word?
Europeans look on in dismay at how the world’s once-leading democracy has utterly lost the plot and slides in accelerating fashion toward societal models that we tried in the 1930s and 1940s and found seriously wanting. We’ve seen this movie and know how it ends; with way too many people in scary uniforms and lots of barbed wire everywhere.
The Dutch Example
Those lessons are particularly instructive for us Dutch. Since the mid-1600s, Amsterdam was a refuge for ethnic and religious groups from all over Europe who fled various forms of repression and persecution. This freedom and societal diversity was one reason why the Dutch trading empire flourished with technological advances (such as wind-powered sawmills for fast boat-building) and economic (corporate and stock) innovations.
The tolerance and diversity helped the Netherlands develop into a conflict-avoiding nation of traders who got along with everyone so they could sell them stuff. We kept out of World War I and sold a lot of planes to Germany. Municipalities registered people’s religion and ethnicity for a range of practical (and mostly benign) purposes such as allowing the local civil servants to operate in a culturally sensitive way.
The Dutch government kept this fantasy of remaining neutral going for a long time, right up to the early morning of May 10, 1940, when the German Wehrmacht rolled into the country and swept away our poor excuse for an army in barely four days. After the Dutch surrender, the vast majority of the German army was pulled out of the Netherlands and put to work in other places.
For the vast majority of Dutch people life went on pretty much as before. Resistance to the occupation was almost non-existent and many Dutch were happy to work for the government (the number of civil servants almost doubled during the occupation) or in industries that boomed because of orders from the German army.
It was not until 1942 that the enthusiastic data-collection by the Dutch government turned into a human catastrophe. Over 100,000 people – who thought they “had nothing to hide” – had provided accurate data on their Jewish identity and listed their addresses, enabling the most complete persecution of Jewish people in any country during World War II (with the exception of Poland where the Nazis had more time and fewer logistical challenges).
The other problem was the pro-authority attitude of most Dutch (even if that authority was a brutal military occupation by a foreign army). The famous Dutch “tolerance” often expressed itself as “I don’t care what you do as long as you don’t bother me.” That included shoving fellow citizens into cattle-cars on their way to death-camps. There was no occupied country where Pastor Martin Niemoller’s famous poem – “first they came for the Socialists…” – was more applicable than the Netherlands.
Troubling Comparisons
Though comparisons with the Nazi era are always problematic, aspects of that time and U.S. society today are eerily similar. The United States seems under the de facto control of a consortium of banksters and an military-industrial-security complex begging for blood, all feeding off each other and feeding into a political/media system that controls the national agenda and marginalizes people who dissent.
This structure has made many citizens afraid of their own shadows and lacking the information to ask meaningful questions even if they so desired. There are two political parties, the minimum number to have at least the pretense of a democracy, but – on issues relating to “national security” and the “surveillance state” – the Republicans and Democrats offer little that is significantly different, except at the fringes of the two parties.
Sen. Feinstein’s blasé acceptance of the National Security Agency’s collection of electronic metadata on virtually everyone and President Barack Obama’s mild “reforms” of the NSA fit with what you can expect from many “security-conscious” Republicans, too.
Yet, the unpleasant reality is that the U.S. government has built a turnkey infrastructure for a level of totalitarian control that repressive leaders of past eras could only dream about. The NSA’s metadata lets the government chart a spider’s web of your associations with multiple “hops” to draw in the networks of other people whom you have never met. The scheme takes guilt-by-association to whole new levels.
The U.S. government also reserves to itself the right to kill anyone, anywhere who supposedly represents a “terrorist” threat to the United States – and to do so on the say-so of some unaccountable and essentially anonymous intelligence officials.
A Political Excuse
The only missing element for a full-scale tyranny is a political excuse to flip the switch and turn this machine on full-power. Perhaps the excuse could come from another “terrorist attack” or from another financial meltdown as the government seeks to control social unrest. Or a thoroughly unscrupulous President might just rev it up to go after his enemies. But the point is the equipment is now in place and ready to go.
Many people still find it hard to accept that the U.S. government could take such a monstrous turn. But its modern history – from Hiroshima through the Vietnam War to support for death-squad regimes in Latin America and the invasion of Iraq – shows a callous disregard of human life and an acceptance of mass slaughter, even genocide, as a policy choice.
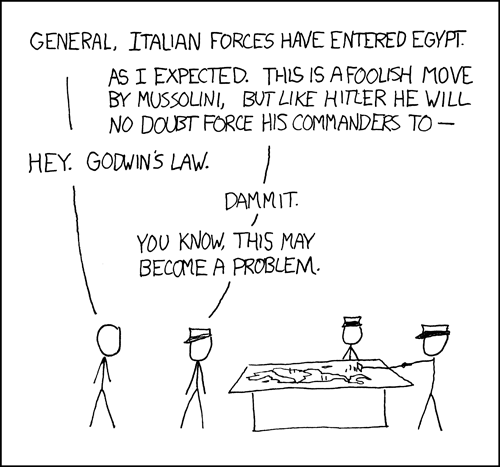 I realize that these concerns that I’ve raised violate what’s known as “Godwin’s Law”, i.e. the avoidance of comparing current events to the Nazis, but – regrettably – these comparisons are increasingly unavoidable. One could even revise Niemoller’s famous poem for the present:
I realize that these concerns that I’ve raised violate what’s known as “Godwin’s Law”, i.e. the avoidance of comparing current events to the Nazis, but – regrettably – these comparisons are increasingly unavoidable. One could even revise Niemoller’s famous poem for the present:
First they came for the Muslims in a dozen countries
but most of us did not share that faith so we said nothing
Then they came for union leaders and social activists
but we did not want to be labeled as lefties and so we said nothing
Then they came for the journalists
but we long stopped reading political news and so we said nothing
Then finally, when the government came for us
there was no one left to say anything”
Arjen Kamphuis left his native Netherlands (an active participant to the warcrimes in Afghanistan & Iraq) over 5 years ago for Germany – the one country that has learned deep lessons from trying out various forms of totalitarian regimes.
‘Tinfoil Is The New Black’, Keiser Report interview
I was a guest on Max Keiser’s programme ‘The Keiser Report‘ last Thursday jan. 16th for the second time. Max is a former Wall Street trader who foresaw the current economic crisis a decade ago.
Full Keiserreport episode here on RT site and here on Youtube.
Max caught me be susprise by asking about the NSA TURMOIL and TURBINE programs. I confused them with other programs (there are many). The TURMOIL and TURBINE programs are part of the ‘Targeted Acces Operations’ family (see this Spiegel article). These are programs for gaining acces to systems by other means than abusing their built-in weaknesses over internet connections (the NSA’s favourite method because it can be automated to spy on everyone at very low cost). Targeted Accces Operations (TAO) deals with everything from intercepting & modifying electronic devices that people order online to the use of microwave beam weapons to identify, hack, break and manipulate computer systems from great distance. The latter method has also been used for targeting drone strikes. The talk by Jacob Appelbaum I mention in the beginning of the interview is here. Many more talks from the 2013 CCC conference in Hamburg can be found here.
The US Declaration Of Independence is one of the greatest political writings in history and can be re-written for more contemporary political problems as I did here. Accoring to US academics the US declaration was inspired by the Dutch declaration that preceded it by almost two centuries.
Blogpost on a previous interview last year.

 Nederlands
Nederlands
 English
English
